The OWASP Top 10: Broken Authentication & Session Management
Did you know a whopping 113 million websites contain a security vulnerability? That’s approximately six percent of all websites globally.
A website vulnerability is a weakness in website code that cybercriminals can exploit to gain unauthorized access to a site—and a mere one vulnerability has the power to impact over 1,000 pages on a single website.
Let’s talk about one of the most common types of vulnerabilities on the OWASP Top 10: broken authentication and session management. Simply stated, broken authentication and session management allows a cybercriminal to steal a user’s login data or forge session data, such as cookies, to gain access to websites.
What is the OWASP Top 10?
The OWASP Top 10, short for Open Web Application Security Project, is a list of the ten most dangerous web application security flaws today (including broken authentication and session management). According to owasp.org, its purpose is to drive visibility and evolution in the safety and security of the world’s software. As of 2021, broken authentication is now referred to as identification and authentication failures by OWASP.
What is broken authentication and session management?

Many websites require users to log in to access their accounts, make a purchase, etc. More often than not, this is done using a username and password. With this information, a site will assign and send each logged-in visitor a unique session ID that serves as a key to the user’s identity on the server.
If not properly secured, a cybercriminal can impersonate a valid user and access that user’s account, resulting in a broken authentication and session management attack.
How can the authentication process be exploited?
When a user logs onto a website, the site uses a proprietary algorithm to generate a unique session ID. Their device then uses that session ID as a key to their identity for the remainder of their user session.
All of this information has to be sent back and forth between the user and the server. If that information is not encrypted and is sent as plain text instead, it becomes an attack vector. Hackers can then intercept user credentials or session IDs to impersonate that person. This is especially true when operating on a public network (e.g. coffee shop wifi) or a public computer that anyone else can access. The following are some broken authentication and session management attack examples.
Credential stuffing
The stealing of usernames and passwords to gain unauthorized access to user accounts across multiple websites and services is known as credential stuffing. This technique relies on the fact that many people reuse the same login credentials across different online platforms. Attackers typically obtain these credentials from breaches of other websites and then use automated tools to test them on various websites in hopes of finding matches. Credential stuffing exploits the widespread issue of password reuse and can lead to unauthorized access to user accounts, compromising sensitive information, and leading to financial or reputational damage.
Brute force attacks
Another approach a cybercriminal could take is attempting a brute-force attack wherein they repeatedly try common weak passwords to guess a user’s correct password. It is also possible for attackers to forge session IDs if they are not randomly generated. For example, if an attacker intercepts several legitimate session IDs that are enumerated, it is possible to guess the next legitimate session ID and access the site fraudulently. These are commonly referred to as man-in-the-middle attacks.
Password spraying attacks
This type of cyberattack uses a single password against many user accounts before moving on to another password to avoid triggering account lockouts. This technique contrasts with brute force attacks, which try many passwords against a single user account. Password spraying targets the common use of weak passwords across multiple accounts and takes advantage of the fact that many users opt for simplicity over security. By exploiting the likelihood that at least some accounts will use common passwords, attackers can gain unauthorized access without alerting the authentication mechanisms designed to lock accounts after a few unsuccessful login attempts.
How to prevent broken authentication attacks
Explore below broken authentication best practices to protect user credentials and authentication processes from exploitation by bad actors.
Use an SSL certificate
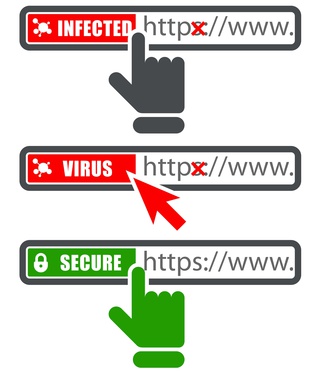
To prevent man-in-the-middle type attacks on your site’s sessions, it is important to encrypt this data in transit using an SSL certificate. As the name implies, an SSL (secure socket layer) is a digital certificate that encrypts information sent between a web server and a web browser.
Enforce strong passwords
Regarding brute force attacks, mentioned earlier in this article, it’s a good practice to have access control and password policies for any and all registered users on a site (this includes admin accounts, especially!).
Strong passwords do not have complete words; instead, they consist of a combination of random letters (both uppercase and lowercase), numbers, and symbols to prevent users' passwords from being easily guessed. Minimum password lengths should also be required, and users should be required to update their passwords after multiple failed login attempts are detected.
Use a session manager
Implement a secure, server-side session management system that creates a new, random session ID with high complexity each time someone logs in. Ensure the session ID is not visible in the web page's URL, is kept safe, and is properly discarded following a user's logout, periods of inactivity, or after session timeouts.
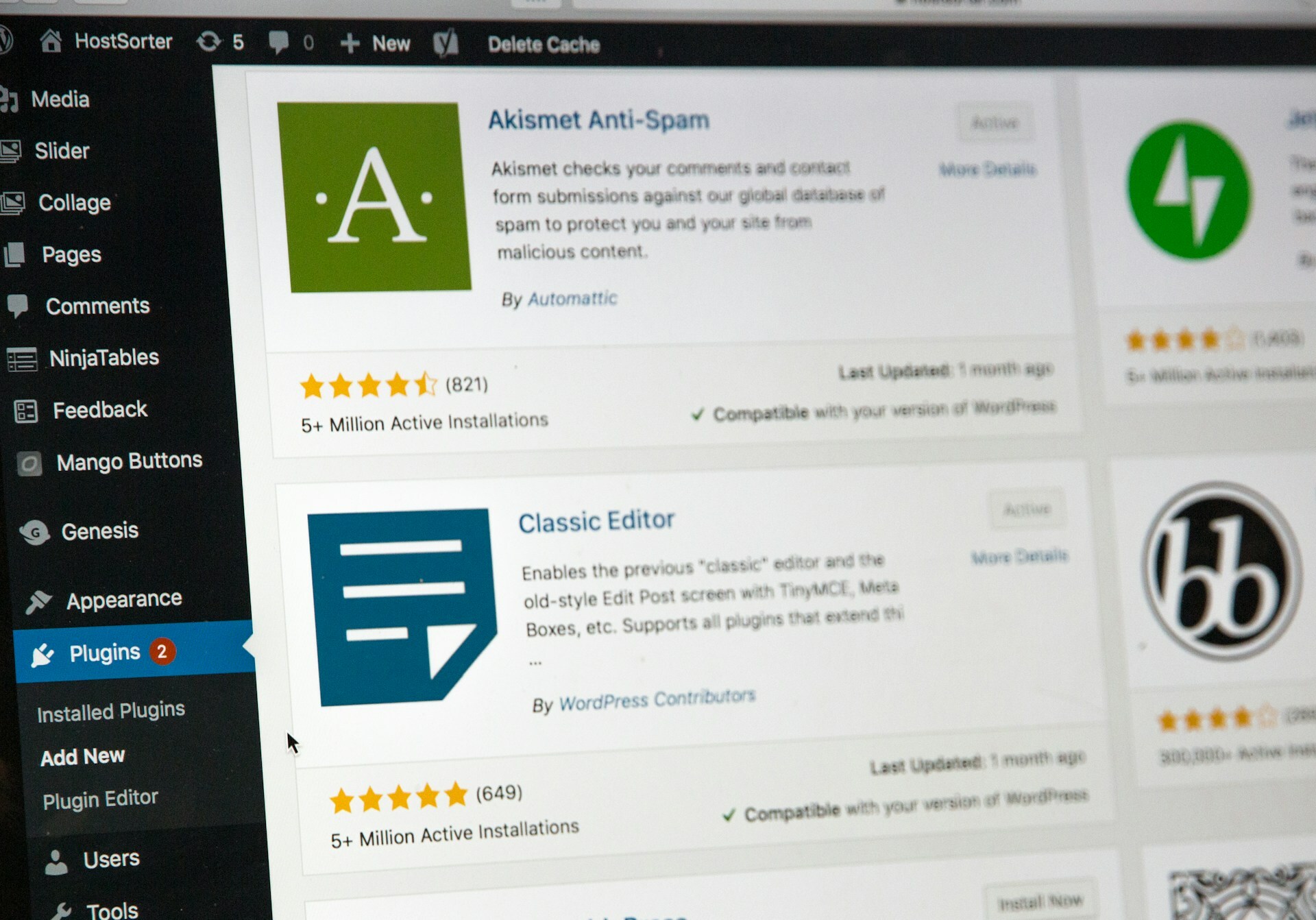
Conduct regular website security audits
Make sure you are on top of any website vulnerabilities or issues by conducting security audits on a regular basis. An automated website security plan is also helpful in that it continuously monitors the site for issues.
Prevent data breaches with SiteLock
In short, broken authentication and session management is a major security risk. It can allow a hacker to steal a user’s sensitive data or forge session data, such as cookies, to gain unauthorized access to websites. However, there are simple and easy solutions to prevent your site from being affected by this vulnerability. Learn more about protecting your site with our website security solutions. If your site has already been hacked, discover how SiteLock's website hack repair service can help.